Explore Our Core Capabilities
Device Teardown
Physical disassembly of electronic devices to document internal components and manufacturing methods.

Semiconductor X-Ray Teardown
Non-destructive X-ray imaging to analyze internal chip structures and detect counterfeit components.

Layer 7 PDU Capture and Analysis
Application-layer data analysis to uncover communication behavior, APIs, and security insights.

Wi-Fi 802.11x Family Analysis
Protocol-level assessment of Wi-Fi performance, security, and compliance in wireless devices.

App Reverse Engineering
Decompilation of mobile apps to reveal core logic, security flaws, and proprietary features.

Layer 2–4 PDU Capture and Analysis
Network packet inspection across lower OSI layers to assess protocol integrity and connectivity.

Handset Compliance Testing
Regulatory evaluation to ensure telecom devices meet global safety and interoperability standards.

Source Code Review
Thorough code inspection to identify bugs, vulnerabilities, and IP risks before deployment.

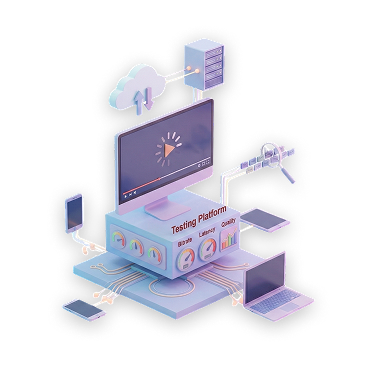
Media Streaming Testing
Evaluation of streaming quality, DRM, and platform performance across varied devices and networks.

Meet the Future of IP Validation with Agility & Confidence
Intellect Partners
Your IP claims require irrefutable evidences. We deliver it. Through expert led reverse engineering, our team provides the technical evidence to strengthen your litigation, licensing, and monetization efforts. Our deep expertise spans today's most complex sectors, from Hi-Tech, Semiconductor, Telecommunication to Medical Devices.

Device Teardown
Precise, methodical disassembly of electronic devices to identify, document, and analyze internal components, materials, and manufacturing techniques. Our teardown process reveals hardware architecture, component selection matters.

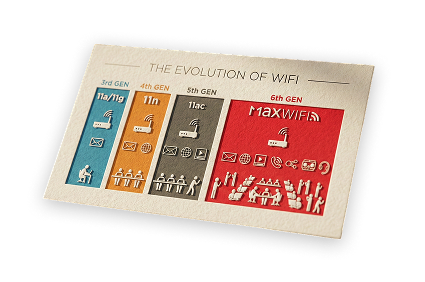
Wi-Fi 802.11 x Family Analysis
Our protocol-level analysis assesses the core of a product's Wi-Fi 802.11 implementation. We benchmark RF performance, scrutinize security protocols, and measure data transfer efficiency to provide critical competitive insights and essential evidence for IP validation.
Handset Compliance Testing
De-risk your product launch with our comprehensive compliance testing. We validate your device against global telecommunication and safety standards, ensuring full interoperability and functionality to prevent costly delays and guarantee market readiness.

Semiconductor X-Ray Teardown
A non-destructive analysis method utilizing high-resolution X-rays to visualize the internal structure and composition of semiconductor components and integrated circuits without physical disassembly.
App Reverse Engineering
Protect your digital assets and enforce your IP rights. Our app reverse engineering process analyzes compiled code to identify critical security vulnerabilities, expose hidden data trackers.
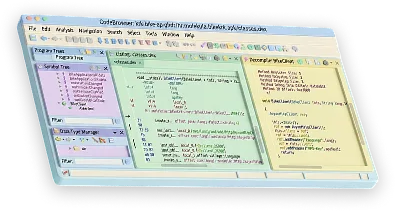

Source Code Review
Fortify your technology before it goes live—and before it is exposed in enforcement or defense. Our systematic source-code review identifies security vulnerabilities, functional gaps, and inefficient implementations.
Layer 2-4 PDU Capture and Analysis
Establish or challenge infringement through packet-level evidence. By capturing and analyzing live and recorded traffic across the data-link, network, and transport layers.
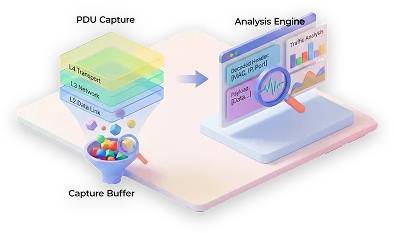
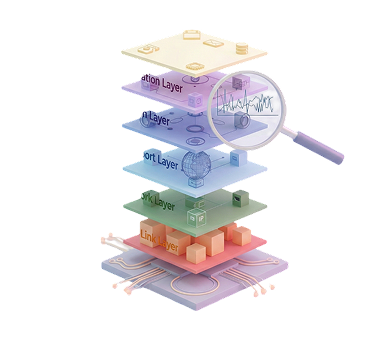
Layer – 7 PDU Capture and Analysis
Reveal application-level communication behavior with evidentiary precision. Our application-layer traffic analysis examines API calls, message exchanges.
Media Streaming Testing
We analyze real-time media delivery, DRM enforcement, and platform behavior under load to confirm that accused streaming services practice the patented techniques.
Integrated RE Capabilities Across Domains
Hardware & Semiconductor RE
- Chip-level teardowns
- Core monitoring & profiling
- Emulator & base station testing

Telecom & Wireless RE
- Spectrum and protocol analysis
- Wi-Fi (802.11x) & LTE investigations
- RRC capture & essentiality checks

Claim Charting & IP Support
- SEP essentiality checks
- Claim chart creation (Wi-Fi, telecom, media)
- Evidence-of-use validation & case studies

Case Studies & Outputs
- Real-world claim chart examples
- Sample packet captures & decoded datasets
- Anonymized success stories & deliverables

Software & Application RE
- Source code decompilation & analysis
- App behavior & process monitoring
- Virtual execution & sandbox testing

Media & Streaming RE
- Streaming protocol testing (HLS, CDN, m3u8)
- Codec identification & benchmarking
- Data packet tracing (Wireshark, Fiddler)

Infrastructure & Test-Beds
- Specialized RE labs & secure environments
- Spectrum analyzers, emulators, protocol analyzers
- Automated & custom test-bed setups

Technical Domains & Service Areas
- Layer 2–7 protocol decoding
Call tracing & signaling analysis
Cross-platform RE for handsets & IoT devices

Why Partner With Us for Reverse Engineering?
 1. Competitive Intelligence & Benchmarking
1. Competitive Intelligence & Benchmarking
We deconstruct competitor products to provide a complete intelligence picture. Our analysis reveals their design choices, component sourcing, and technology stack, allowing you to benchmark performance and identify strategic opportunities to outperform them in the market.
 2. IP & Patent Litigation Support
2. IP & Patent Litigation Support
Our reverse engineering provides the irrefutable, forensic-level evidence needed for high-stakes IP disputes. We generate detailed claim charts and Evidence of Use (EoU) reports that clearly demonstrate infringement, strengthening your position in litigation and licensing negotiations.
 3. Security & Vulnerability Assessment
3. Security & Vulnerability Assessment
Uncover critical security flaws before they can be exploited. We analyze hardware, software, and firmware to identify vulnerabilities, insecure data transmissions, and potential backdoors, providing a clear roadmap for remediation to protect your assets and your users.
 4. Manufacturing & Cost Analysis
4. Manufacturing & Cost Analysis
Go beyond functionality to understand the economics of any device. Our teardowns produce a detailed Bill of Materials (BOM) analysis, estimating component and manufacturing costs to inform your pricing strategy, supply chain negotiations, and cost-reduction initiatives.
 5. Accelerating Innovation & R&D
5. Accelerating Innovation & R&D
Shorten your development cycle by learning from existing technologies. We identify novel design techniques and efficient architectures, providing your R&D team with the insights to avoid costly engineering mistakes and build a superior product, faster.
 6. Interoperability & Compatibility Analysis
6. Interoperability & Compatibility Analysis
Ensure your product works seamlessly within its intended ecosystem. We reverse engineer communication protocols and undocumented APIs to provide the technical blueprint needed for developing compatible, interoperable products or third-party add-on services.
The Intellect Library
At Intellect Partners, we believe knowledge empowers innovation. u2028Our Resource Hub is your free destination to explore Intellectual Property, Technology, and Innovation insights.
From protection to growth—
your first step is reaching out.